
Category: Threat Intel Reports
-
Coinbase phishing email tricks users with fake wallet migration
A large-scale Coinbase phishing attack poses as a mandatory wallet migration, tricking recipients into setting up a new wallet with…
-
SocGholish’s Intrusion Techniques Facilitate Distribution of RansomHub Ransomware
MalwareSocGholish’s Intrusion Techniques Facilitate Distribution of RansomHub Ransomware=================================================================================Trend Research analyzed SocGholish’s MaaS framework and its role in deploying RansomHub ransomware…
-
Malicious PyPI Packages Stole Cloud Tokens-Over 14,100 Downloads Before Removal
Cybersecurity researchers have warned of a malicious campaign targeting users of the Python Package Index…
-
Appellate court upholds sentence for former Uber cyber executive Joe Sullivan
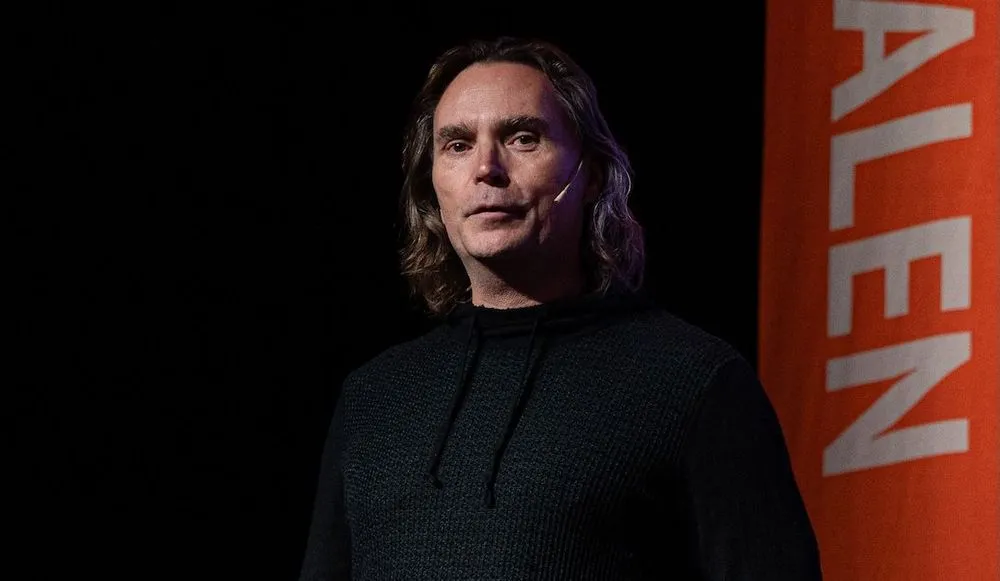Joe Sullivan speaks at the 2024 Sikkerhetsfestivalen conference in Norway. Image: Wikimedia Commons / Arve Synd…
-
Threat Actor Impersonates Booking.com in Phishing Scheme
 [Alexander Culafi,…
-
ClickFix: How to Infect Your PC in Three Easy Steps
A clever malware deployment scheme [first spotted in targeted attacks last year](https://krebsonsecurity.com/2024/09/this-windows-powershell-phish-has-scary-potential/) has now gone mainstream. In this scam, dubbed…
-
Man-in-the-Middle Vulns Provide New Research Opportunities for Car Security
 [Kristina Beek, Associate Editor,…
-
Ransomware Developer Extradited, Admits Working for LockBit
 [Kristina Beek, Associate Editor,…
-
From South America to Southeast Asia: The Fragile Web of REF7707
While the REF7707 campaign is characterized by a well-engineered, highly capable, novel intrusion set, the campaign owners exhibited poor campaign…
-
U.S. CISA adds six Microsoft Windows flaws to its Known Exploited Vulnerabilities catalog
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds six Microsoft Windows flaws to its Known Exploited Vulnerabilities catalog.———————————————————————————————————————————————The U.S. Cybersecurity…

