A clever malware deployment scheme [first spotted in targeted attacks last year](https://krebsonsecurity.com/2024/09/this-windows-powershell-phish-has-scary-potential/) has now gone mainstream. In this scam, dubbed ‘**ClickFix** ,’ the visitor to a hacked or malicious website is asked to distinguish themselves from bots by pressing a combination of keyboard keys that causes **Microsoft Windows** to download password-stealing malware.ClickFix attacks mimic the ‘Verify You are a Human’ tests that many websites use to separate real visitors from content-scraping bots. This particular scam usually starts with a website popup that looks something like this: 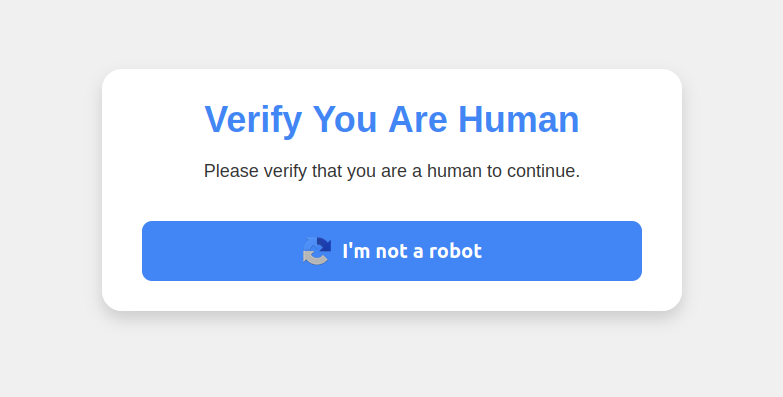This malware attack pretends to be a CAPTCHA intended to separate humans from bots.Clicking the ‘I’m not a robot’ button generates a pop-up message asking the user to take three sequential steps to prove their humanity. 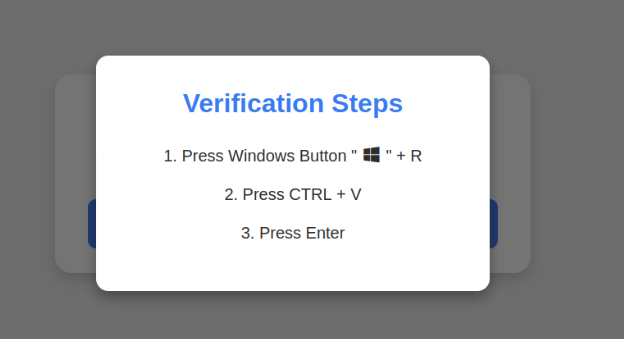Executing this series of keypresses prompts Windows to download password-stealing malware.Step 1 involves simultaneously pressing the keyboard key with the Windows icon and the letter ‘R,’ which opens a Windows ‘Run’ prompt that will execute any specified program that is already installed on the system.Step 2 asks the user to press the ‘CTRL’ key and the letter ‘V’ at the same time, which pastes malicious code from the site’s virtual clipboard.Step 3 — pressing the ‘Enter’ key — causes Windows to download and launch malicious code through ‘**mshta.exe**,’ a Windows program designed to run Microsoft HTML application files.’This campaign delivers multiple families of commodity malware, including XWorm, Lumma stealer, VenomRAT, AsyncRAT, Danabot, and NetSupport RAT,’ **Microsoft** wrote in [a blog post](https://www.microsoft.com/en-us/security/blog/2025/03/13/phishing-campaign-impersonates-booking-com-delivers-a-suite-of-credential-stealing-malware/) on Thursday. ‘Depending on the specific payload, the specific code launched through mshta.exe varies. Some samples have downloaded PowerShell, JavaScript, and portable executable (PE) content.’According to Microsoft, hospitality workers are being tricked into downloading credential-stealing malware by cybercriminals impersonating **Booking.com** . The company said attackers have been sending malicious emails impersonating Booking.com, often referencing negative guest reviews, requests from prospective guests, or online promotion opportunities — all in a bid to convince people to step through one of these ClickFix attacks.In November 2024, KrebsOnSecurity reported that hundreds of hotels that use booking.com had been subject to targeted phishing attacks. Some of those lures worked, and allowed thieves to [gain control over booking.com accounts](https://krebsonsecurity.com/2024/11/booking-com-phishers-may-leave-you-with-reservations/). From there, they sent out phishing messages asking for financial information from people who’d just booked travel through the company’s app.Earlier this month, the security firm **Arctic Wolf** [warned](https://arcticwolf.com/resources/blog/healthcare-sector-targeted-by-fake-captcha-attack-on-hep2go-to-deliver-infostealer-malware/) about ClickFix attacks targeting people working in the healthcare sector. The company said those attacks leveraged malicious code stitched into the widely used physical therapy video site HEP2go that redirected visitors to a ClickFix prompt.An [alert](https://www.hhs.gov/sites/default/files/clickfix-attacks-sector-alert-tlpclear.pdf) (PDF) released in October 2024 by the **U.S. Department of Health and Human Services** warned that the ClickFix attack can take many forms, including fake **Google Chrome** error pages and popups that spoof **Facebook**. 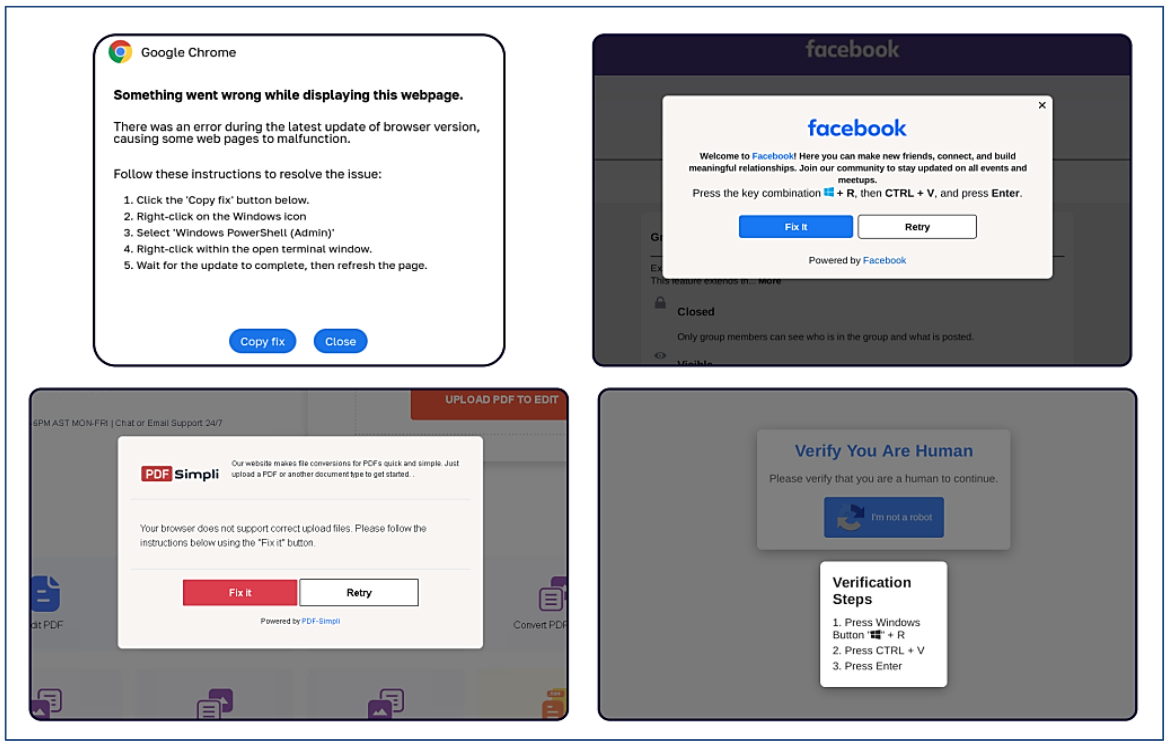ClickFix tactic used by malicious websites impersonating Google Chrome, Facebook, PDFSimpli, and reCAPTCHA. Source: Sekoia.The ClickFix attack — and its reliance on mshta.exe — is reminiscent of phishing techniques employed for years that hid exploits inside **Microsoft Office** **macros**. Malicious macros became such a common malware threat that Microsoft was forced to start blocking macros by default in Office documents that try to download content from the web.Alas, the email security vendor **Proofpoint** has [documented](https://www.proofpoint.com/us/blog/threat-insight/security-brief-clickfix-social-engineering-technique-floods-threat-landscape) plenty of ClickFix attacks via phishing emails that include HTML attachments spoofing Microsoft Office files. When opened, the attachment displays an image of Microsoft Word document with a pop-up error message directing users to click the ‘Solution’ or ‘How to Fix’ button. 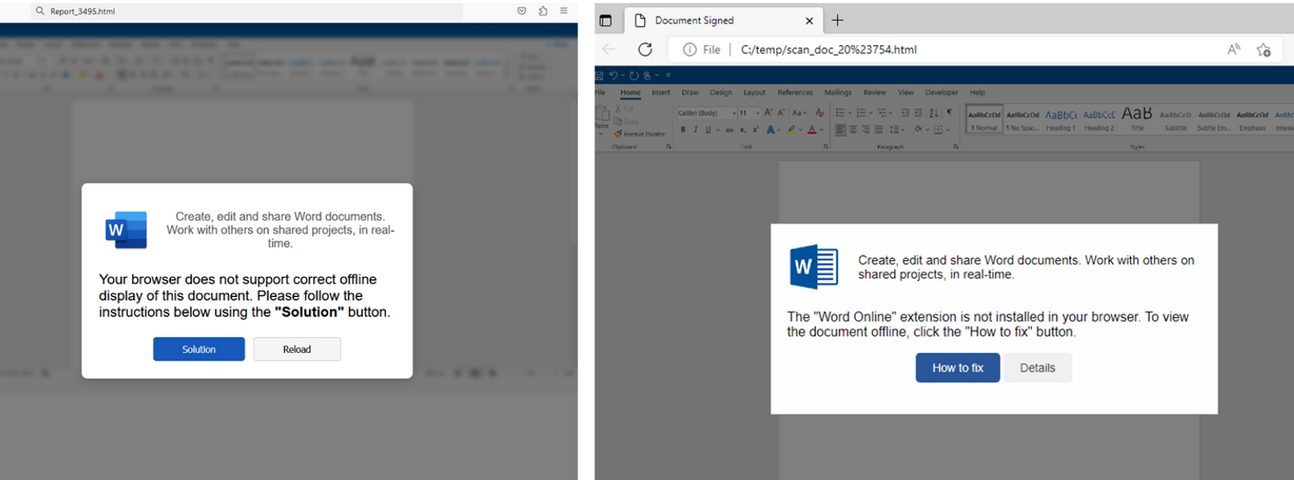HTML files containing ClickFix instructions. Examples for attachments named ‘Report_’ (on the left) and ‘scan_doc_’ (on the right). Image: Proofpoint.Organizations that wish to do so can take advantage of [Microsoft Group Policy restrictions](https://m.majorgeeks.com/content/page/disable_run_command.html) to prevent Windows from executing the ‘run’ command when users hit the Windows key and the ‘R’ key simultaneously.
Related Tags:
NAICS: 923 – Administration Of Human Resource Programs
NAICS: 72 – Accommodation And Food Services
NAICS: 519 – Web Search Portals
Libraries
Archives
Other Information Services
NAICS: 517 – Telecommunications
NAICS: 541 – Professional
Scientific
Technical Services
NAICS: 518 – Computing Infrastructure Providers
Data Processing
Web Hosting
Related Services
NAICS: 92 – Public Administration
NAICS: 516 – Broadcasting And Content Providers
NAICS: 721 – Accommodation
Associated Indicators:


